
Protect Your Digital Future with Softuvo
Secure what matters most—your data, systems, and people—with intelligence-led data security and AI-driven defense strategies.
The Threats Are Evolving.
Is Your Defense Keeping Up?
Cyber resilience is no longer about perimeter firewalls. It's about foresight.
Modern enterprises face:
- Expanding attack surfaces due to rapid digital adoption
- AI-powered and automated cyberattacks
- Fragmented visibility across cloud and hybrid environments
- Increasing global compliance pressure
Softuvo combines AI and cybersecurity to transform reactive defense into predictive protection, reducing breach risks by up to 40% and response times by 60%.
The future of data security requires intelligence, automation, and continuous adaptation.
What Is Threat Detection & Response?
Threat detection & response is a proactive cybersecurity strategy that identifies suspicious activity in real time and neutralizes threats before operational damage occurs.
Unlike traditional monitoring, AI-powered detection systems analyze:
Network Traffic
Analyzing network behavior
User Patterns
Access pattern monitoring
Endpoint Activity
Real-time device monitoring
Cloud Security
Hybrid environment safety
This enables automated containment, forensic analysis, and rapid remediation, minimizing disruption and preventing data breaches.
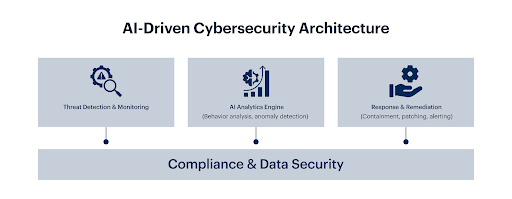
Softuvo's Intelligent Cybersecurity Framework
We secure every digital layer of your organization through an integrated model built on three core pillars.
Threat Detection & Response
Detect and respond to threats before they impact your operations.
AI-powered threat intelligence and monitoring systems analyze network behavior, user activity, and endpoint data in real time, enabling automated detection, containment, and remediation of security threats.
Data Protection
Ensure confidentiality, integrity, and availability of critical business data.
Multilayered protection safeguards customer and proprietary data across on-premise, cloud, and hybrid environments using encryption, access control, and zero-trust architecture to keep information secure wherever it resides.
Compliance & Governance
Align operations with global regulatory frameworks effortlessly.
Meeting global data regulations like GDPR, HIPAA, and ISO 27001 is complex. Compliance is simplified through automated monitoring, policy alignment, and ready-to-use audit reports, ensuring every standard is met with confidence.
Strengthening Email & Domain Security with YourDMARC
Softuvo extends data security protection through YourDMARC, our advanced DMARC monitoring and email authentication platform.
Measurable Security Outcomes
Softuvo enabled enterprises to modernize cybersecurity architecture and transition from reactive defense to predictive protection.
Faster incident detection & response
Reduction in manual security operations
Audit readiness for regulated industries
Data loss incidents in protected environments
Protecting Innovation
with Intelligence
At Softuvo, cybersecurity is about enabling innovation without compromise. With expertise across cloud, AI, and data governance, we design solutions that scale securely as your business grows.
Our Differentiators:

Insights That Strengthen Cyber Resilience
Stay ahead of emerging threats with our latest cybersecurity perspectives.
How Do Growing Businesses Decide Between SaaS and Custom Software?
Why Businesses Need Intelligent Automation to Stay Competitive in 2026
Incident Response Management for Email Compliance: Essential Steps
IoT Email benefits and security risks

Ready to Fortify Your
Digital Ecosystem?
Design a security strategy that protects what matters and powers your next phase of growth.